AWS Secret Manager is a secrets management service provided by Amazon Web Services (AWS). It allows you to securely store and manage secrets, such as database credentials, API keys, and other sensitive information.
In 01Cloud, the AWS Secret Manager can be used as an external secret provider, which means that 01Cloud can fetch and use the secrets stored in AWS Secret Manager. This allows you to centralize the management of sensitive information and access the secrets from multiple applications, including those running in a Kubernetes environment.
By using the AWS Secret Manager in 01Cloud, you can improve the security and reliability of your applications by separating the secrets from the code and reducing the risk of hardcoded secrets in the codebase. Additionally, you can also easily update the secrets without having to update the code.
You can explore more about external secret in 01Cloud here.
Steps to create AWS Secret
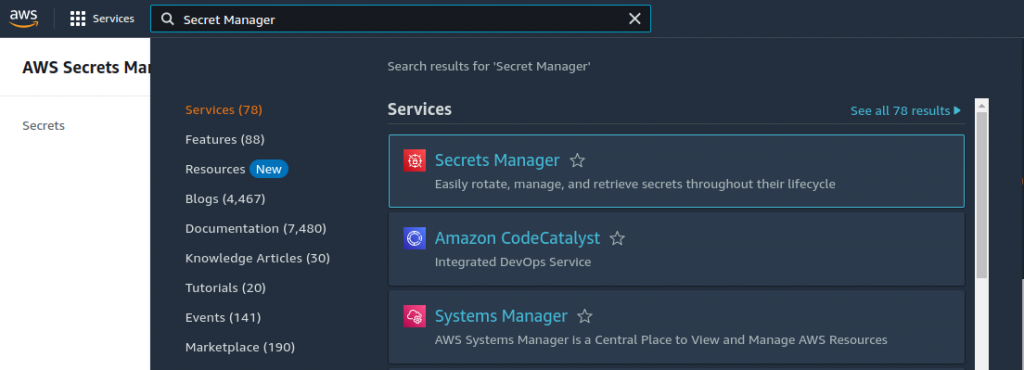
- To start, let’s create a secret in AWS Secret Manager. Begin by searching for the “Secrets Manager” service in the search bar and opening it.
- Click on Store a new secret.
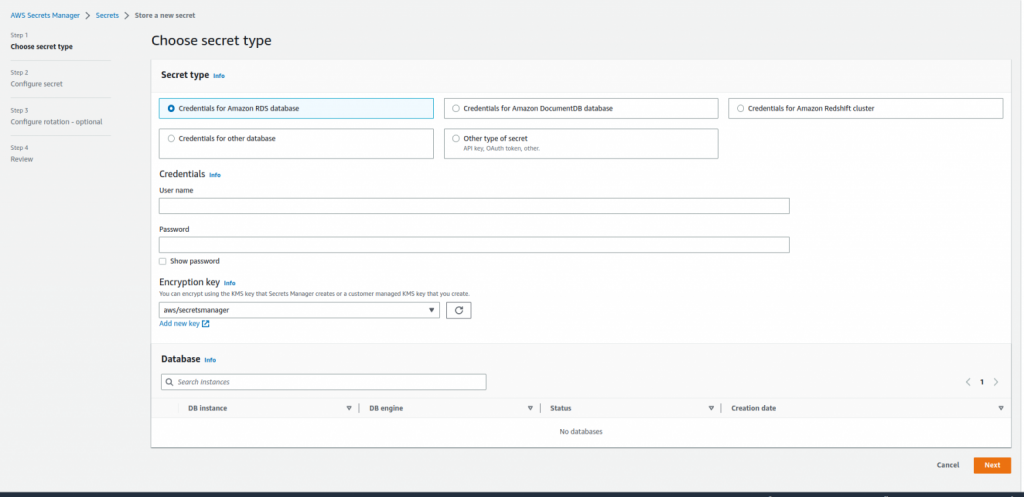
- This type of interface will open and insert the value. We will create a key/value pairs secret and store different key/value secret. Click on next and configure secret and finally store a new secret.
- We have created two secret wordpress-secret and other-secret.
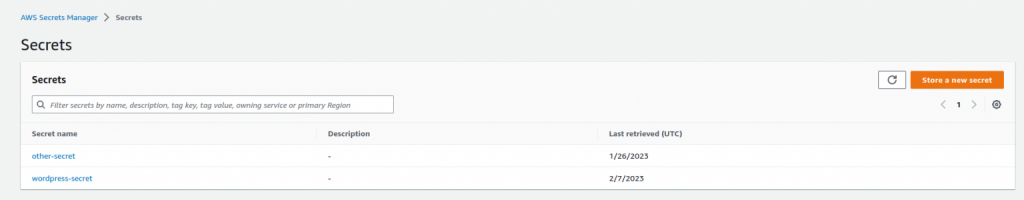
- we will retrieve the stored secret using 01Cloud’s external secret service and use it within our 01Cloud application. In order to do so, when generating the AWS Secret and Access Key, we must ensure that the “secretsmanager:GetSecretValue” permission is granted.
Steps to use AWS Secret in 01Cloud
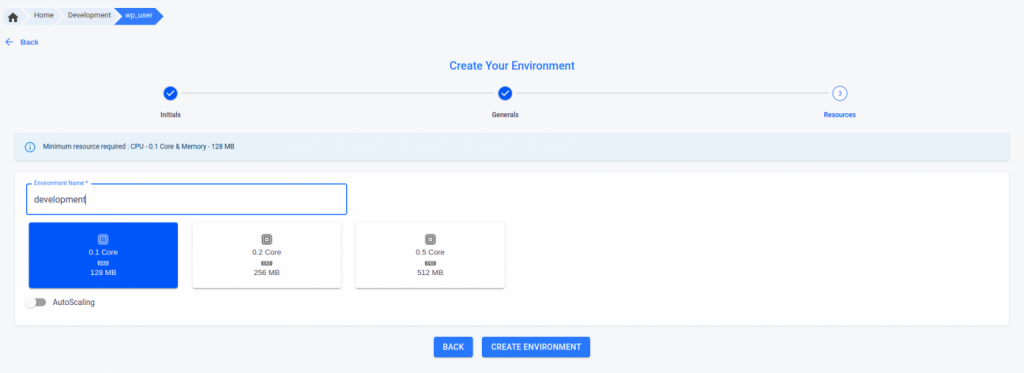
- At first we have created a development project and inside the project we have created a wordpress application named wp_user.
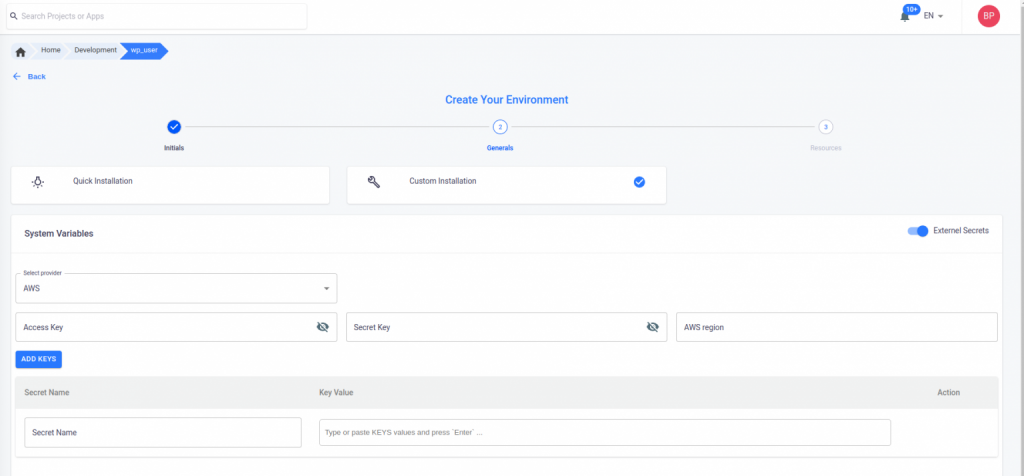
- When creating the environment, it is necessary to enable External Secrets in the Custom Installation section. Upon enabling, you must fill in the necessary fields.
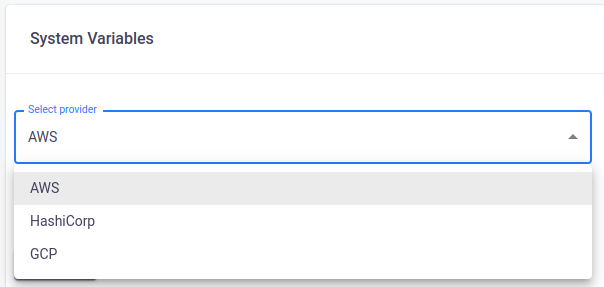
- Currently, in 01Cloud there three providers available i.e AWS(Amazon Web Service), HashiCrop Vault and GCP(Google Cloud Platform). You can select any of three from Select Provider field.
- The fields are primarily used for authentication. For instance, when using AWS, you will need to provide the Access Key, Secret Key, and AWS region. There is also a field labeled “Secret Name” where you specify the name of the secret created in your external secret manager (in this case, AWS Secret Manager). The “Key Value” field is optional, but you can specify the specific keys you want to retrieve. If left blank, all the keys in the external secret will be retrieved.
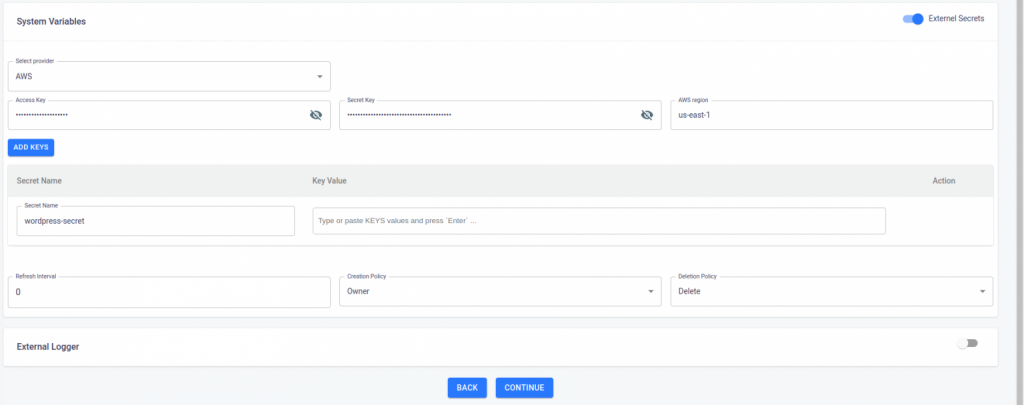
- Now we can continue our environment creation process.
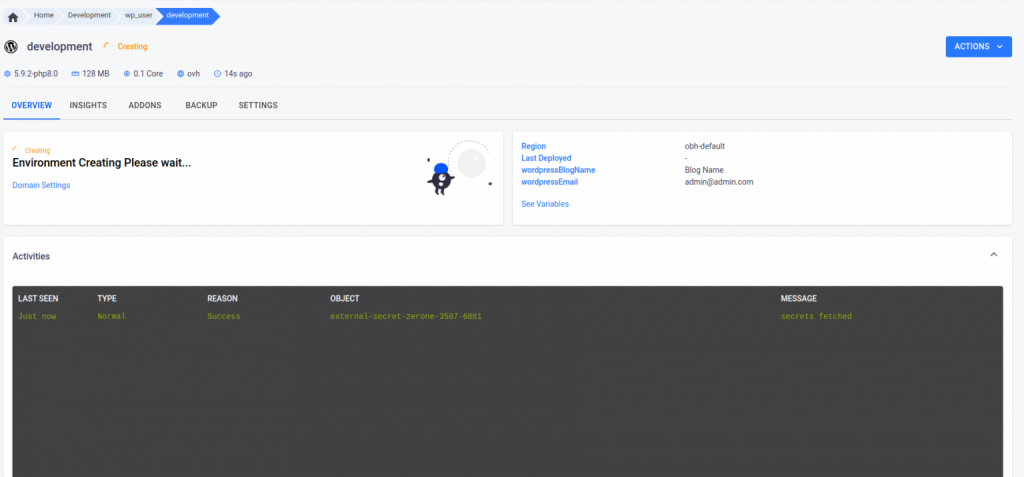
- Once the environment creation process has been initiated, the authentication information provided in the external secret will be processed. If the authentication is successful, you should see a message indicating that the secret has been retrieved in the activity log within your environment.
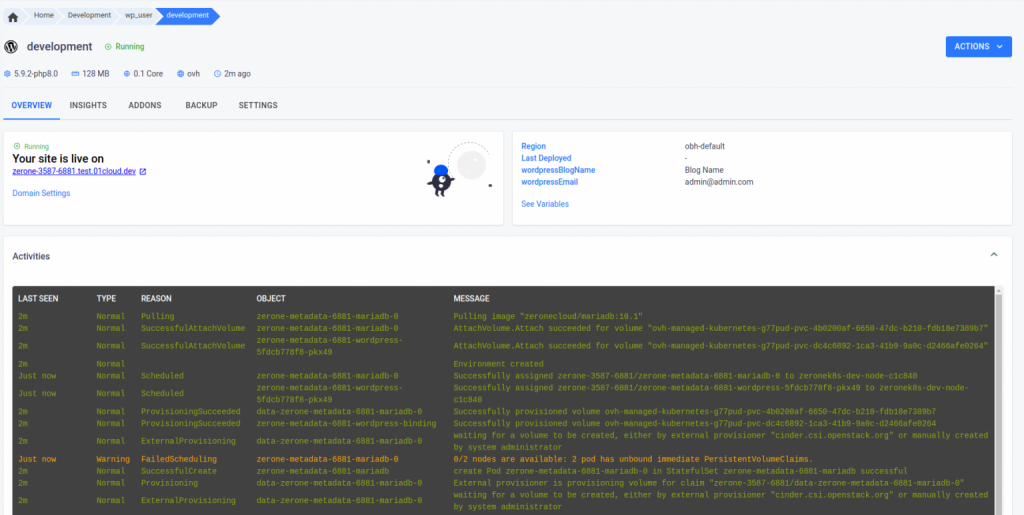
- As we can see our environment is running.
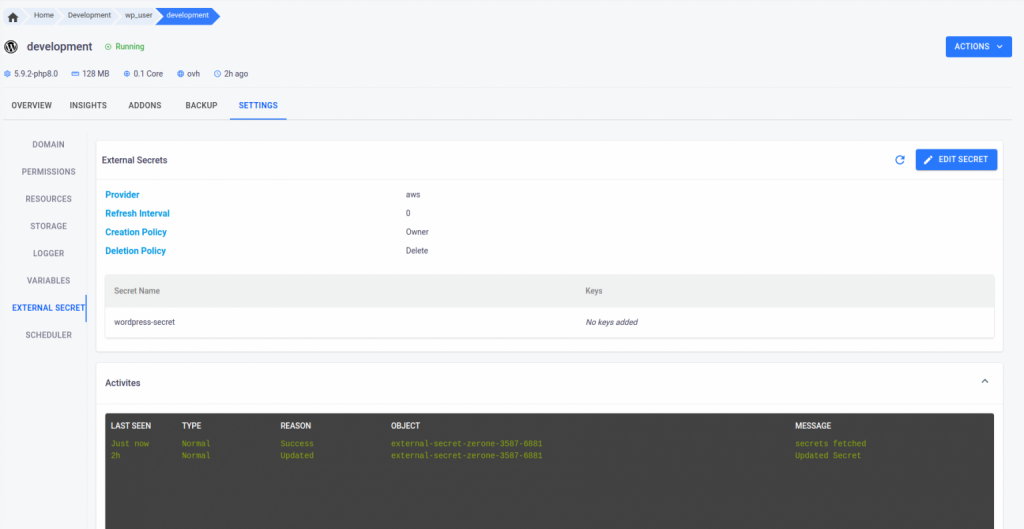
- You can view the details of the external secret in the External Secret tab located in the settings. Additionally, you have the option to edit the secret and manually force the external secret operator to retrieve the data once again from the external secret manager.
Conclusion
In this manner, you can set up and utilize the External Secret feature in 01Cloud. 01Cloud retrieves and employs the information gathered from the external secret, integrating it into the 01Cloud environment.